QUICK GUIDE
Thank you very much for installing Browser Sentinel. This quick guide enables you to easily get started with Browser Sentinel.
- What Audience Does Browser Sentinel Target?
- What Browser Sentinel Does And What It Doesn't
- To Delete Or Not To Delete?
- System Items
- Safe and Blocked Lists
- Tags
- Data Update
- Critical Zones
What Audience Does Browser Sentinel Target?
 |
Browser Sentinel targets experienced users who understand the way Windows functions. The program lets a user edit very "sensitive" (or critical) zones of Windows. On one hand, this allows you to get complete control over these zones, accepting or denying any changes there. On the other hand, rough/casual/unskilled handling of these zones can lead to serious consequences for your system (e.g. data loss or a need for Windows to reinstall). Please BE VERY CAREFUL when using Browser Sentinel. If you don't feel you are sufficiently experienced, please consult an IT professional before taking any actions using Browser Sentinel. |
|
The critical zones are divided into two groups: Internet Explorer and System. The zones from the Internet Explorer group affect only Internet Explorer and won't harm your system even if you do something wrong. The worst thing that can happen is that a third-party software re-installation may be required, in case you deleted a legitimate item. You can freely make changes in these zones even if you're a novice user. |
 |
 |
The zones from the System group directly affect crucial parts of Windows and thus must be handled very carefully. Unless you are a highly skilled programmer, it is highly recommended that you read the corresponding help topic before making changes to the System group zones. |
What Browser Sentinel Does And What It Doesn't?
 |
Browser Sentinel displays information about critical zones of Windows, which can be abused by malicious software (malware: adware, spyware, trojans, etc.) with the purpose of watching your activity, displaying popup ads or spamming your computer. Having these zones monitored by Browser Sentinel lets you always be informed of malware activity on your computer. Browser Sentinel also lets you counteract malware by editing these critical zones. Browser Sentinel does NOT have a malware database. It won't tell you what program is legitimate and what program is not. It is up to you to decide what is malware and what is not. Browser Sentinel displays exhaustive information about every item in the zone. Armed with your intuition and a good search engine you should have no problem finding and destroying the parasites! |
To Delete Or Not To Delete?
|
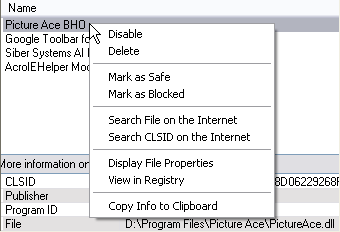
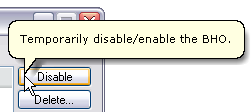
Generally, Browser Sentinel lets you take one of the two actions: Disable or Delete. The Disable action temporary deactivates an item, but lets you activate it again later. The Delete action permanently removes an item from your system. When possible try to always disable an item before permanently deleting it. Please note that sometimes you may need to reboot Windows or restart Internet Explorer to enable/disable certain items. |
 |
System Items
 |
Browser Sentinel contains a small built-in database of system items, i.e. the items that ship with Windows and are a part of it. Having system items hidden lets you find third-party items more easily. Please note that the database includes only the most frequently used system items and cannot be considered as a complete system items database. The chances are that some valid system items of some version of Windows will be detected by the program as non-system items. This can be the case after installing an update, a service pack or an addition. Special versions of Windows can also include system items not included in the program database. This means that you should not take as gospel the system items database. Use it only as a helper function, not as the ultimate authority. |
Safe and Blocked Lists
|
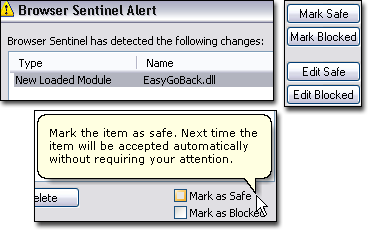
There are legitimate programs that regularly change the contents of the critical zones. For example, a program adds and removes itself to/from the startup programs list in the registry. Another program regularly adds/removes its items to/from the Internet Explorer context menu. Since Browser Sentinel alerts you every time the contents of a zone is changed, it can become very annoying having to accept such changes each time they occur. The safe item lists let you designate items that you fully trust (so Browser Sentinel will not warn you when an item from a safe list is added to a zone.) But there are cases when you might want to delete items every time a program adds them to a critical zone. Blocked item lists let you designate items that you want to be deleted or disabled every time they're added to a zone. |
 |
Tags
  |
If you want to mark an item or a group of items with a custom description you can use tags. A tag is displayed in the item properties and can be searched for.  A tag can be entered when the alert window is show. You can also add or edit a tag by right-clicking an item and selecting Edit Tag.  |
Data Update
 |
It takes time for Browser Sentinel to gather information about all critical zones of your system. During this time, the title of the program's main window changes to "Updating data. Please wait...". You should not take any actions while the data update is in progress. If you want to force the data update, hit the F5 key or use the tray icon menu or the Options tab. |
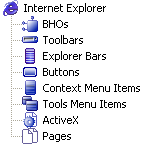
Critical Zones
BHOs. A Browser Helper Object (BHO) is an extension/plugin for Internet Explorer that extends the browser's functionality. It is a DLL module that is loaded by Internet Explorer each time it starts up.
Toolbars. A toolbar is an extension/plugin for Internet Explorer that extends the browser's functionality and displays a custom toolbar underneath Internet Explorer's main menu and navigation bar.
Explorer Bars. An explorer bar is a panel usually shown on the left of the browser window, e.g. Search, History, Favorites, etc. Apart from displaying various useful information, an explorer bar can also track IE events, modify web page text, open new browser windows, etc.
Buttons. An IE toolbar button is an IE extension that adds a new button on the IE toolbar next to the standard buttons (Go Forward, Go Back, etc.).
Context Menu Items. A context menu item is a third-party menu item that appears in the Internet Explorer context menu.
Tools Menu Items. A Tools Menu item is an entry in the Internet Explorer Tools Menu. The item can execute various actions (starting a program, showing/hiding an explorer bar, etc.)
ActiveX. An ActiveX is a component (usually a DLL or an OCX module) that provides better interaction with web site pages than those using only HTML. For instance, an ActiveX control can display video/animation, play sounds, render dynamic 3d graphics, etc.
Pages. Default pages (start page, search page, error pages, etc.), search URLs and URL prefixes for Internet Explorer.
Startup Programs. A startup program is a program that is started automatically at Windows startup.
Running Programs. A running program is a program that is currently loaded in the memory and is executing.
Services (not available in 98/ME). A service is an executable application that runs in its own Windows session. A service can be automatically started when the computer boots, can be paused and restarted, and does not show any user interface. Services are used to implement long-running functionality that does not interfere with other users who are working on the same computer.
Drivers (not available in 98/ME). A device driver is a component that Windows uses to provide I/O services for and interact with an underlying device, such as a modem or network adapter. Rather than access the device directly, Windows loads device drivers and calls functions in the drivers to carry out actions on the device. The driver functions contain the device-specific code needed to carry out actions on the device. Drivers are sometimes used by various keylogger/spyware software to record system events.
Loaded Modules. Loaded modules are dynamic link libraries (DLL files) that are currently loaded in the BrowserSentinel.exe process. This zone is very effective in detecting keylogger software since keyloggers usually inject their DLL files into a process to monitor keystrokes using the Windows hooking technique.
Startup Modules. Startup modules are dynamic link libraries (DLL files) that are loaded automatically during Windows startup or later when a particular application starts. Browser Sentinel defines six startup module types: ShellExecute Hook, Shell Delay Load Object, App Init DLL, URL Search Hook, Custom Download Manager and Notification Package.
Shell Extensions. A shell extension is a DLL module that extends Windows Explorer functionality. Most shell extensions just add new entries to the Windows Explorer context menu - the menu that appears when you right-click on a file or a folder.
HOSTS file. The HOSTS file contains hostnames and their mappings to an IP address. This file is often abused by malicious programs that set up a redirection from certain popular web sites (e.g. Google.com) to web sites they want you to visit.
LSPs. An LSP is a piece of software that can be inserted into the chain of data transferring software on your computer. Before data from a web server reaches your web browser, it goes through all the chained software, including installed LSPs. The same is true for outgoing data. Malicious software can use LSPs to see all traffic being transported over your Internet connection.
Protocols. An asynchronous pluggable protocol can be used to handle a custom Uniform Resource Locator (URL) protocol scheme, filter data for a designated MIME type or intercept requests transmitted over existing protocols (e.g. http, https, ftp). Sophisticated malware can use this technique to watch your Internet activity.